The cybersecurity landscape in Australia witnessed a surge in phishing attacks during 2022-2023, underscoring the pervasive threat of social engineering tactics. These incidents demonstrate that organisations of all sizes remain vulnerable to such manipulative schemes. Notably, a significant proportion of these attacks targeted high-ranking individuals, emphasising the sophisticated nature of modern cyber threats.
We advocate for a proactive cyber culture by providing phishing exercises. These exercises serve as valuable tools for continuously evaluating and improving cyber defences. By simulating real-world phishing attacks, organisations can better understand their vulnerabilities and take necessary steps to mitigate risks.
Our Experiences with Phishing Exercises
What is Phishing?

In simple terms, phishing is a type of social engineering where attackers use deceptive messages, often via email, to trick individuals into reveal sensitive information or installing malware. It preys on human psychology, making everyone a potential target.
The Phishing Exercise
Our Cyber Security team conducted a phishing exercise to test vigilance against potential cyber threats. This exercise mimicked communication from a CEO, sending emails from an external Gmail address tailored to each recipient. The goal was to assess awareness and responses to potential phishing threats.
To enhance this exercise, the team developed a ‘Malicious Cues and Payload Difficulty Rating’ matrix. This system graded the difficulty of phishing emails to measure and improving the workforce’s discernment skills.
Phishing Email Construction
- Sender Impersonation: The email appeared to be from a CEO but originated from an external Gmail account, testing if employees could spot the red flag in the sender’s identity.
- Personalisation: Each email was personalised to increase legitimacy, testing recipients’ ability to scrutinise seemingly familiar requests.
- Content: The email requested recipients to review a resume in a Word document, supposedly from a CEO-recommended candidate, exploiting human tendencies like curiosity and the desire to assist.
- Security Alert: Despite its authentic appearance, a subtle warning banner indicated the sender’s external status, assessing employees’ attention to detail and adherence to email security protocols.
Results and Analysis
The exercise provided insightful findings:
- 65% of participants were compromised, highlighting the need for increased awareness and training.
- 47% correctly identified and reported the email as malicious, demonstrating the effectiveness of ongoing security awareness efforts.
- 29% incorrectly reported the phishing attempt, posing a potential internal threat by spreading malicious content.
- 71% of users who completed Defence Security Awareness training were compromised, suggesting the need for more targeted training.
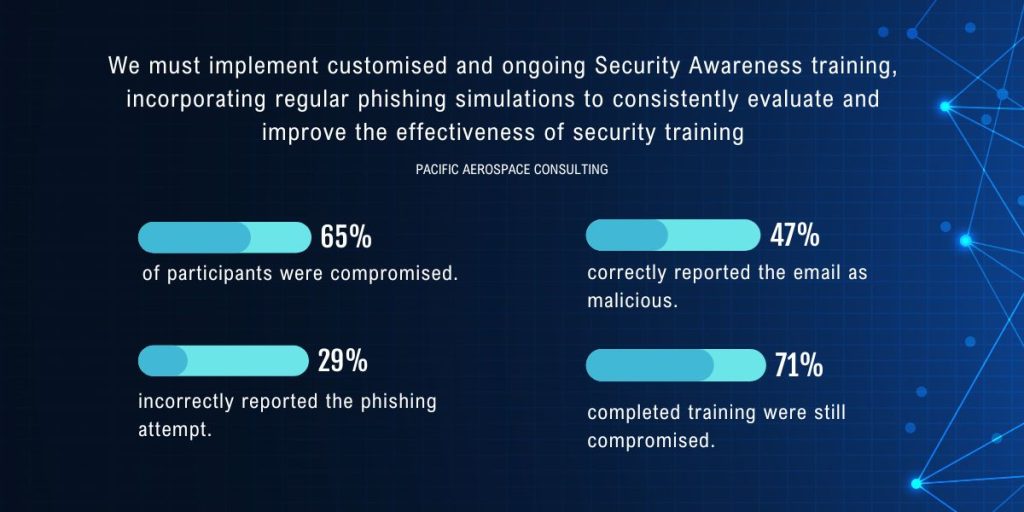
Lessons Learned and Recommendations
The outcomes emphasise the need for customised and continuous Security Awareness training with regular phishing exercise to continually assess and enhance security training effectiveness.
ASD Cyber Threat Report 2022-2023
The ASD Cyber Threat Report outlines the increasing costs and evolving nature of cybercrime in Australia. Average cybercrime costs have surged, underscoring the critical importance of robust cybersecurity measures. Beyond immediate costs, the report highlights the threats of reputational damage and erosion of customer trust. Key takeaways include cybercriminal adaptability, the prominence of email compromise and online banking fraud, and a significant rise in ransomware and extortion-related incidents.
Building a Culture of Cyber Literacy and Resilience
Acknowledging mistakes are part of the human experience, our Cyber Security team focuses on support and improvement outcomes, with an emphasis on the importance of fostering a company-wide culture of cyber awareness and preparedness. Leadership plays a pivotal role in promoting this culture, ensuring every team member is equipped with the necessary tools and mindset for active participation in the organisation’s cyber defence.
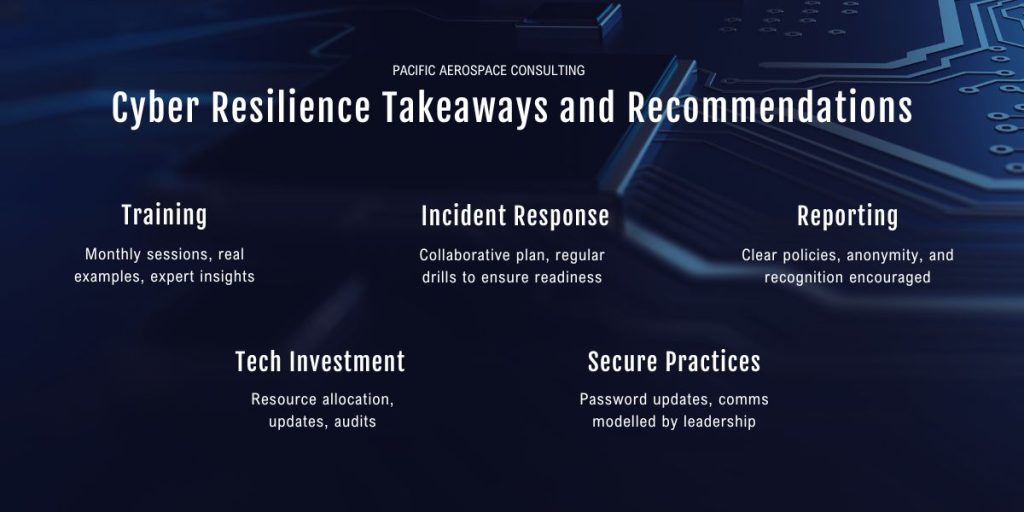
Regular Training Sessions
Leaders can initiate and participate in regular cyber awareness training sessions for the entire team, ensuring that everyone stays updated on the latest cyber threats and best practices.
- Schedule monthly or quarterly cybersecurity training sessions for all team members.
- Introduce real-life case studies to illustrate potential risks.
- Bring in external experts for specialised training on emerging threats and prevention strategies.
Lead by Example
Leadership can demonstrate a commitment to cybersecurity by consistently following recommended protocols. This includes using secure communication channels, regularly updating passwords, and adhering to other cybersecurity measures.
- Regularly update passwords and encourage the team to do the same.
- Use secure communication channels and insist on their usage within the team.
- Share personal experiences of adhering to cybersecurity measures during team meetings.
Encourage Reporting
Leaders should create an environment where team members feel comfortable reporting potential security threats without fear of reprisal. This proactive reporting helps in early detection and mitigation of potential cyber risks.
- Communicate a clear policy on reporting potential security threats and incidents.
- Establish an anonymous reporting system to encourage those who may be hesitant to come forward.
- Recognise and commend team members who proactively report potential threats.
Incident Response Plan
Develop and communicate a clear incident response plan. Leaders can ensure that the team knows the steps to take in case of a cyber incident, fostering a sense of readiness and a structured approach to handling threats.
- Collaborate with IT and Security teams to develop a comprehensive incident response plan.
- Conduct regular drills or exercise to ensure the team is familiar with the plan’s execution.
- Provide accessible documentation outlining the steps to be taken in case of a cyber incident.
Investment in Technology
Leadership can allocate resources for robust cybersecurity technologies. This includes advanced threat detection systems, secure communication tools, and regular security audits to stay ahead of evolving cyber threats.
- Allocate budget for the purchase and regular updating of advanced threat detection systems.
- Implement secure communication tools and ensure team-wide adoption.
- Schedule regular cybersecurity audits to identify vulnerabilities and address them promptly.
Integrating cyber security into everyday business practices involves regular updates to security protocols, staying informed about the latest threats, and ensuring staff are equipped to identify and respond effectively to threats. Practical implementation of cyber security controls aligned with the ASD Essential Eight is essential for reducing vulnerability to cyber-attacks and building a resilient and security-aware culture.
Conclusion
As we navigate high-risk periods like the holiday season, maintaining continuous awareness and adaptability is crucial. The phishing exercise serves as a powerful reminder of the importance of heightened vigilance. It underscores the need for ongoing enhancement of security training and awareness as cyber threats evolve. Businesses are urged to take proactive measures, not only by implementing technological solutions but also by educating and empowering their workforce. Fostering a culture of cyber literacy and resilience is paramount for building robust defences against the sophisticated tactics of cybercriminals. Remember: Stay sharp, stay secure!